UVa’s Most Popular Stories of 2008
Monday, December 22nd, 2008The story about Adrienne Felt’s Facebook privacy study made the list of UVA Today Most Popular Stories of 2008.
|
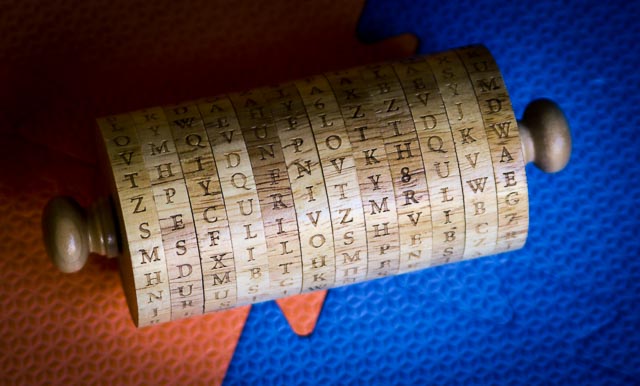
Jefferson's WheelSecurity Research at the University of Virginia |
The story about Adrienne Felt’s Facebook privacy study made the list of UVA Today Most Popular Stories of 2008.
I’m organizing a workshop next week on the “Science of Security”, co-sponsored by the National Science Foundation, IARPA, and the National Security Agency.
The goal of the workshop is to gather a group of about 40 leading scientists and researchers in a diverse range of areas to identify scientific questions regarding computer security, and to stimulate new work toward defining and answering those questions.
For more information, see the workshop website: http://sos.cs.virginia.edu.
This is a guest post by Sarah Scrafford (see below for details). It describes the AntiVirus XP 2008 malware, which is interesting because of the amount of information revealed about its financial success. Another article that provides some more details about this is in the New York Times: Antiviral ‘Scareware’ Just One More Intruder which provides some interesting financial details.
An important anniversary related to computer security recently went by without much publicity – the release of the first ever malicious program to spread widely on the Internet. The year was 1988, the date November 2, and the creator the worm, Robert Tappan Morris, then a student at the Cornell University, unleashed his creation on the Internet and succeeded in disabling 10 percent of all the machines that were online at the time. Although this was a criminal activity and Morris was convicted later of computer fraud, the incident proved to be the launching pad for the intensive research being done in the area of computer security today.
And so the antivirus, antispam and antispyware software packages made their appearance, each one more sophisticated and capable of detecting newer malware than its predecessors, and a whole new industry was born. Today, Morris holds a respectable position as associate professor of computer science at the prestigious MIT, but new and more innovative crooks are still continuing in his footsteps. Rather than write malware to disable systems, deny service or steal information, the conmen have hit upon a novel and almost foolproof method to make users part with their money – by preying on the insecurities (pun intended).
Being fully aware of the mad scramble for antivirus and other security software, a group based in Russia is offering a free application, the Antivirus XP 2008, which they claim to be an antivirus software package. Once the unsuspecting user downloads it to their system, they’re constantly bombarded with security alerts that scare them into thinking their computers are veritable hotspots for viruses and Trojans to hang out. Antivirus XP 2008 recommends a paid upgrade to be able to quarantine or clean these viruses, and this is how the conmen make their money. Another stroke of genius on their part was to rename the software Antivirus XP 2009, and sell it to users as a new and improved version of itself.
The best part of this scam, according to Joe Stewart, director of SecureWorks Inc. which was responsible for bringing this shady operation to light, is that the kingpin has set up a phony company through which affiliates can market the fake antivirus software – true viral marketing in every sense of the word. If you’re aghast at what you’ve read so far, hold on, there’s worse to come. The crooks are making as much as $5 million a year by just scaring people into parting with their money. And if they’re ever caught, they have a slim excuse to cling to – that they’re not aware of the relative uselessness of their program.
It’s all in a day’s work for them; if not this scam, then something else. But for you and me, the legitimate and regular computer users, this should be a wakeup call to be more diligent and choosy in picking a security suite for our systems.
This article is contributed by Sarah Scrafford, who regularly writes on the topic of on line universities. She invites your questions, comments and freelancing job inquiries at her email address: [email protected].
The November/December 2008 Technology Review Hack, How Smart Is a Smart Card?”, describes Karsten Nohl’s work on reverse engineering the Mifare Classic. In includes a video of a card dissolving, and some great images.

The University of Virginia Press has published a book, What Should I Read Next?: 70 University of Virginia Professors Recommend Readings in History, Politics, Literature, Math, Science, Technology, the Arts, and More edited by Jessica Feldman and Robert Stilling, University of Virginia Press, 2008.
The premise of the book is to collect essays from UVa professors that introduce their field to a general audience by recommending five books to read about it. I contributed an essay on computer science, How Computing Changes Thinking [HTML, PDF, 4 pages]. Here’s the blurb for the book:
What Should I Read Next? taps seventy University of Virginia professors in an array of fields for suggestions on how to satisfy this nagging intellectual curiosity. Each contributor recommends five titles that speak to their area of inquiry, providing both a general introduction and commentary on each selection. The results read like a series of personal tutorials: Larry Sabato considers how political power is acquired, used, and held onto; climatologist Robert E. Davis provides a timely navigation of global-warming literature; and Michael Levenson offers five ways to approach James Joyce’s Ulysses. Other topics include how computing changes thinking, the life and afterlife of slavery, understanding cities, and ecstatic poetry. The entries convey the contributors’ expertise but also, more importantly, the enthusiasm, the original kernels of curiosity, that drew these scholars to their life’s work.
Designed for the lifelong learner who wants to branch out from his or her own profession or discipline, these explorations–of art, science, history, technology, politics, and much more–offer an inspiring place to start.
UVa Today has an article about the book: Faculty Reading Recommendations May Guide Book Lovers, Oct 14, 2008.
The full details of the Crypto-1 cipher (initially exposed back in December) have now been released.
They are published in Appendix A of Henryk Plötz’s thesis report: Mifare Classic – Eine Analyse der Implementierung. The thesis is in German, but the algorithm is published as a C program (by Karsten Nohl, Henryk Plötz and Sean O’Neil), so should be understandable to non-German code readers.
Also yesterday, the paper, Dismantling MIFARE Classic, by Flavio D. Garcia, Gerhard de Koning Gans, Ruben Muijrers, Peter van Rossum, Roel Verdult, Ronny Wichers Schreur, and Bart Jacobs of Radboud University Nijmegen, The Netherlands, appeared at ESORICS 2008. This is the paper that was the subject of NXP’s failed lawsuit.
The publication of these details remove any remaining doubts about the insecurity of the Mifare Classic.
News articles:
D-Day for RFID-based transit card systems, c|net News, 6 October 2008.
“Combining these two pieces of information, attacks can now be implemented by anyone,” RFID researcher Karsten Nohl told CNET News. “All it takes is a $100 (card) reader and a little software.”
…
Security systems like the Mifare Classic that are not peer reviewed are not as trustworthy as systems that can be openly analyzed by researchers looking for flaws, Johanson and Nohl said.“Developing your own proprietary security mechanisms and not getting public scrutiny on it does not work,” Nohl said.
Boffins (finally) publish hack for world’s most popular smartcard, The Register, 6 October 2008.
Two research papers published Monday have finally made it official: The world’s most widely deployed radio frequency identification (RFID) smartcard – used to control access to transportation systems, military installations, and other restricted areas – can be cracked in a matter of minutes using inexpensive tools.
The two documents combined mean that virtually anyone with the time and determination can carry out the attacks, said Karsten Nohl, a PhD candidate at the University of Virginia and one of the cryptographers who first warned of the weakness in December.
“Now the weakness that we and others have been talking about for months can be verified independently by really anybody,” he said. “The flip side is that everybody can now attack Mifare-based security systems.”
Over the past six months, many organizations that rely on the Mifare Classic have upgraded their systems, but Nohl said he is personally aware of a “handful” of systems used by government agencies or large multinational companies that have been unable to make the necessary changes because of the logistical challenges of issuing new badges to employees.
“One hopes that just based on the announcement, most operators of critical security systems have adopted other technologies besides Mifare,” Nohl said.
Update: (10 Oct) Another article from the CBC: Security flaw in smart cards poses risk for transit, building access, CBC News, 10 October, 2008.
Fast Company has an article (by Brendan Collins) on Privacy and Security Issues in Social Networking.
The reason social network security and privacy lapses exist results simply from the astronomical amounts of information the sites process each and every day that end up making it that much easier to exploit a single flaw in the system. Features that invite user participation — messages, invitations, photos, open platform applications, etc. — are often the avenues used to gain access to private information, especially in the case of Facebook. Adrienne Felt, a Ph.D. candidate at Berkeley, made small headlines last year when she exposed a potentially devastating hole in the framework of Facebook’s third-party application API (application programming interface) which allows for easy theft of private information. Felt and her co-researchers found that third-party platform applications for Facebook gave developers access to far more information (addresses, pictures, interests, etc.) than needed to run the app.
…
Will there ever be a security breach-free social network? Probably not. “Any complex system has vulnerabilities in it. It’s just the nature of building something above a certain level of complexity,” says professor Evans. According to Felt, the best idea is a completely private social network. “It simply requires that there’s no gossip in the circle, by which I mean one person who sets their privacy settings so low that third parties can use them to get to their friends.”
“Social networks are great fun, and can be advantageous but people really need to understand that it’s complicated world and you need to step wisely,” Cluley says.
Verayo is the second company to announce the "World’s first unclonable RFID tag" based on a physically unclonable function (PUF), after Veratag announced a similar product based on PUF technology. The security claims of these and other PUF-based products seem dubious since the current realization of PUFs defies basic principles of cryptography. The announcement states:
This new RFID chip is based on recently announced breakthrough technology called Physical Unclonable Functions (PUF). PUF technology is a type of electronic DNA or fingerprinting technology for silicon chips that makes each chip unclonable.
It might be besides the point that neither DNA, nor fingerprints are unclonable. The failure of proprietary security, which has been a constant theme on this blog, has led many to conclude that only well-reviewed security primitives can be strong. PUF technology tries to achieve security in exactly the opposite way: the PUF circuit is designed in a way so that not even the designer understands how outputs are derived from inputs. Security-by-obscurity par excellence.
Every circuit, including PUFs, is a deterministic function; the only difference in PUF circuits is that some inputs to the function vary across different tags. For a PUF to be cryptographically strong, one would hence need to show that
PUFs are a wonderful idea for using manufacturing variance constructively, but in their current realization, PUFs fail to convince that they are strong building blocks for security systems.
The Call for Papers for the 30th IEEE Symposium on Security and Privacy, May 17-20 2009 is now available: http://oakland09.cs.virginia.edu/cfp.html (PDF for printing: http://oakland09.cs.virginia.edu/cfp.pdf.
Submissions of research papers, workshop proposals, and tutorial proposals are due Monday, 10 November 2008. Please consider submitting a paper and attending the conference!
Marc Rotenberg, Executive Director of the Electronic Privacy Information Center, has written an opinion piece for the Sacramento Bee on social networking privacy: Online friends at what price?: The point of social networking is to share your personal information with the world, The Sacramento Bee, 20 July 2008.
Many of my friends were surprised when I signed up for Facebook. “Why would a privacy advocate put personal information online?” they asked.
“For the same reason that people use the Internet for e-mail or pick up a telephone to make a call,” I explained. “It’s very useful. Of course, there are real privacy issues. We should understand them and fix them.”
Today Facebook is both very useful and a genuine privacy threat. …
Privacy problems have continued to plague the service. In May 2007, Facebook opened up the network for software developers to create applications such as Scrabulous that appear on Facebook pages. Some of these programs are very cool, but that doesn’t answer the privacy problem. Application developers were given access to the detailed personal information of the user as well as the friends of the user. And that means just about everything in your profile, from relationship status and education history to copies of photos and favorite movies. And amazingly, the data of your friends, who did not sign up to install the program, have their data gathered up by Facebook and sent to the developers.
Earlier this year, researchers at the University of Virginia found that Facebook was providing access to far more personal information than was necessary; in fact, information that the developers were not even seeking. As lead researcher Adrienne Felt pointed out, this was a dangerous security practice because it created unnecessary risks for Internet users.