Latest from Karsten Nohl: POS Security
Wednesday, December 30th, 2015Karsten Nohl (PhD 2009) presented his work (with Fabian Bräunlein and Philipp Maier) on vulnerabilities in payment protocols (the ones studied are widely used in Germany but not in other countries) at the Chaos Communications Congress on December 27.
The work has been widely covered in the press recently. Here are a few sample articles:
- Watch infosec bods swipe PINs, magstripe data from card readers live on stage, The Register, 30 Dec 2015. (I trust the use of “bods” here is some kind of Britishism, not what it means in American.)
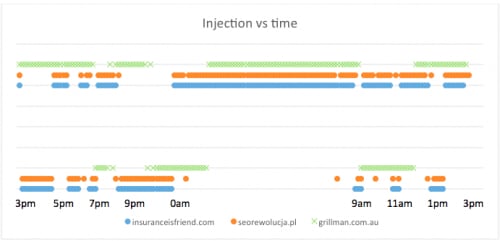
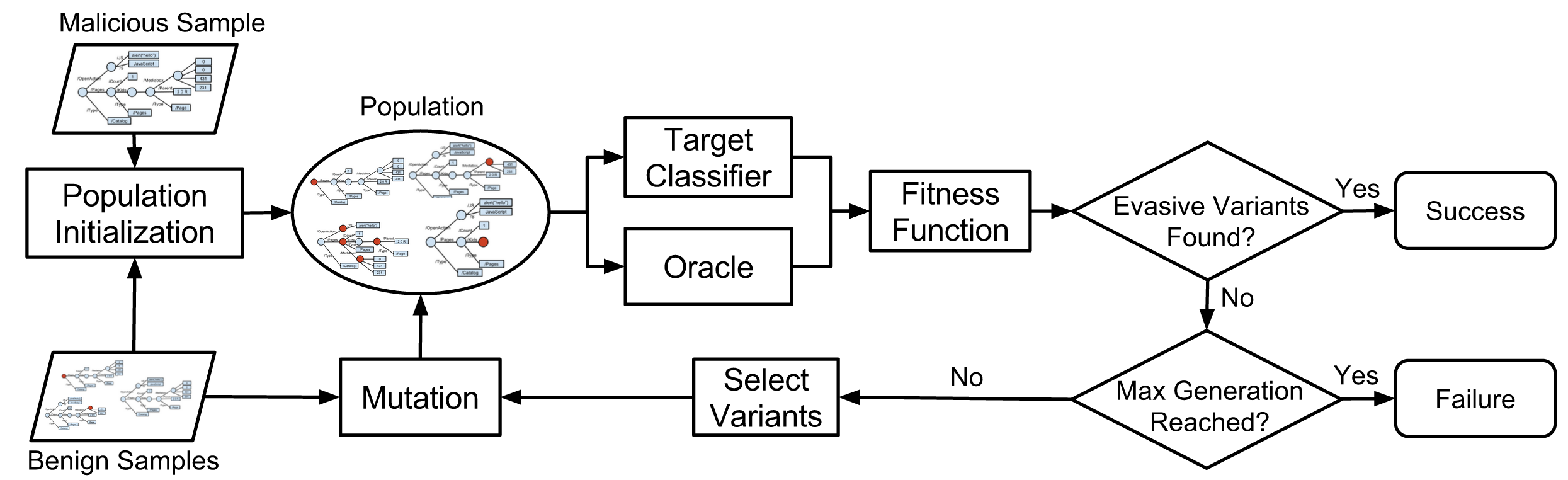
Now let’s look at Poseidon: a crook can buy a Poseidon payment terminal from the internet, and configure it to pretend to be a particular merchant’s systems. To do this, you need three bits of information, which are trivial to obtain…. Now you can perform arbitrary refunds, drawing money from the store’s funds. As there is no interruption to a merchant’s service, the seller will be none the wiser until he or she audits their finances. … German banks have shrugged off their research as merely “theoretical.”
- Payment system security is hilariously bad, BoingBoing (Cory Doctorow), 29 Dec 2015.
- Worries over German retail payments risks, Reuters, 23 December 2015.
A top cyber security researcher has warned German banks that their retail payment systems have security flaws that could allow fraudsters to steal payment card PIN codes, create fake cards or siphon funds from customer or merchant accounts.
Karsten Nohl, who is credited with revealing major security threats in mobile phones, automobiles, security cards and thumb-sized USB drives, told Reuters he has found critical weaknesses in software that runs retail point-of-sale terminals in Germany.