UVa’s Most Popular Stories of 2008
Monday, December 22nd, 2008The story about Adrienne Felt’s Facebook privacy study made the list of UVA Today Most Popular Stories of 2008.
|
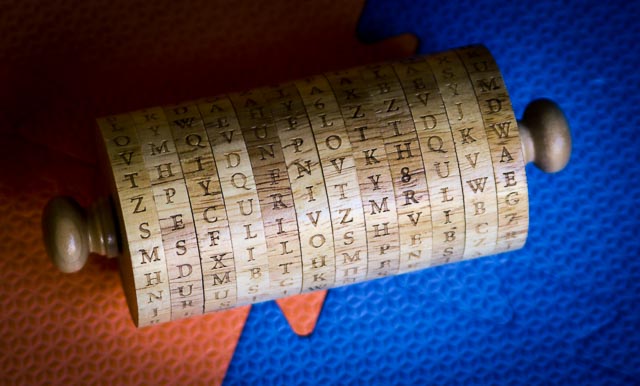
Jefferson's WheelSecurity Research at the University of Virginia |
The story about Adrienne Felt’s Facebook privacy study made the list of UVA Today Most Popular Stories of 2008.
Nathanael Paul’s PhD dissertation has been approved! He will graduate this Sunday.
The dissertation is available here: Disk-Level Malware Detection [Abstract] [Full text: PDF, 155 pages].
Congratulations, Nate! (That is, “Dr. Paul”.) Nate is currently a post-doctoral fellow at Vrije Universiteit, Amsterdam working with Andrew Tanenbaum.
A group at Princeton has released an interesting paper showing that encryption keys can be read from DRAM even after power is lost: Lest We Remember: Cold Boot Attacks on Encryption Keys.
The research team includes Joseph Calandrino, who was a UVa undergraduate student, as well as J. Alex Halderman, Seth Schoen, Nadia Heninger, William Clarkson, William Paul, Ariel Feldman, Jacob Appelbaum, and Edward Felten.
It seems that most encrypted disk drives (any drive where the key is stored in the host’s DRAM) are likely to be vulnerable to this attack. This work seems to provide further support for moving more processing to the disk itself – if the disk processor performs all the encryption and decryption directly, there is no need to move the key into the host memory at all (where this work provides even more evidence that it becomes difficult to protect).
[Added 23 Feb]: New York Times article